Being able to protect your broadband network is essential as your customers are depending on you to protect them from malicious attacks. Unfortunately, Distributed Denial of Service (DDoS) attacks have become increasingly common as they are easy to implement but can be a pain to stop once they’ve launched on your network.
In ZCorum’s effort to help you stay on top of your network activity, below are generic instructions that can provide you with a starting point on changes that can be made to your network to minimize DDoS attacks.
Here’s what you should do first:
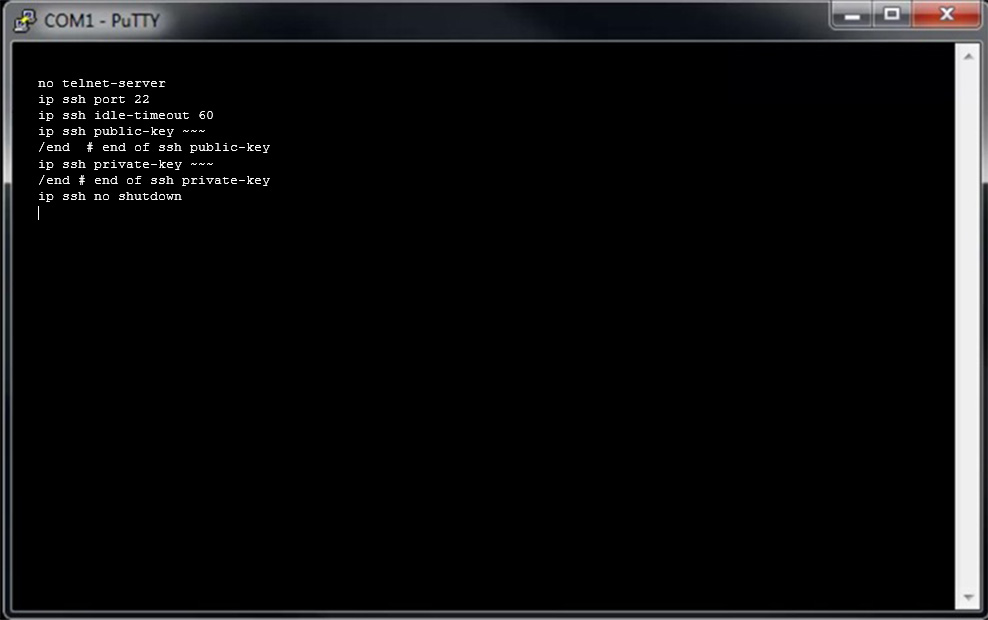
- Lock down equipment login access by removing clear text passwords and enabling SSH access.
- Update ACLs on network edges to only allow access into equipment with trusted IP ranges and deny unknown/untrusted IPs
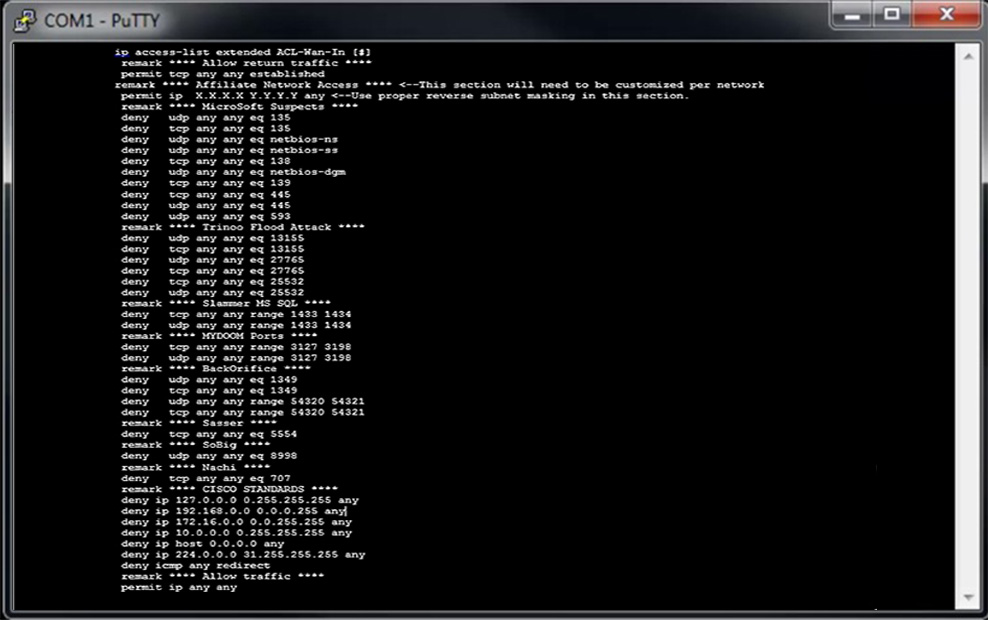
- Update ACLs on network edges to deny access to vulnerable ports
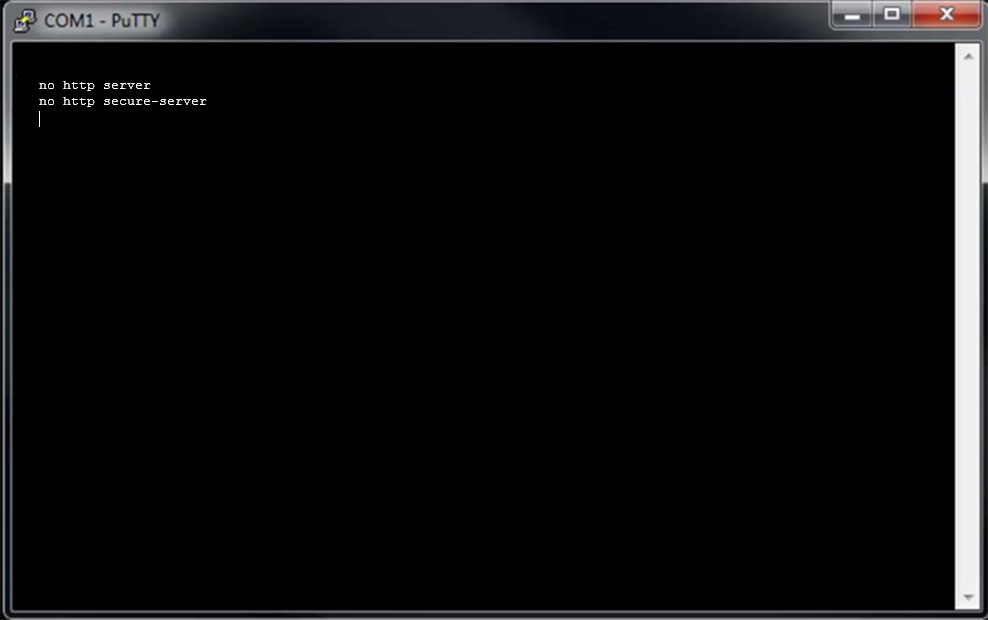
- Remove web configuration access from all equipment on the core network
Generic Examples of Edits Made to the System
Standard Access List Edits
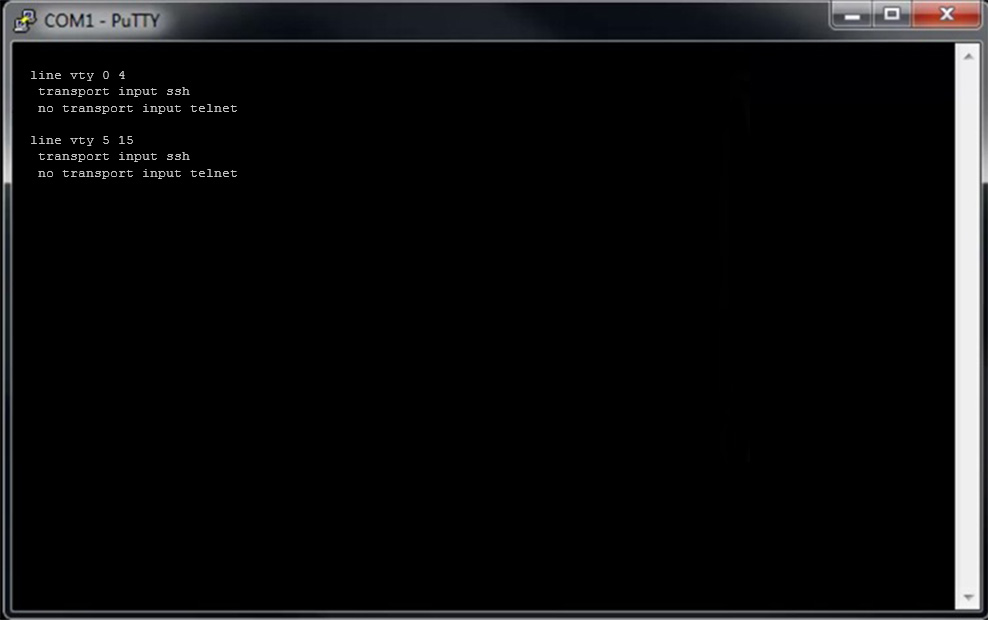
Network wide – REMOVE TELNET ACCESS & APPLY SSH ACCESS on VTY INTERFACES
Network Wide – REMOVE HTTP SERVER and HTTP SECURE SERVER
ACTIVATE SSH and REMOVE TELNET: Standard SSH access is port 22 can be a non-standard port, at network’s discretion